
Security tips
 Critical CPU vulnerability forces Linux users to slow down their computers
Critical CPU vulnerability forces Linux users to slow down their computers
Being a computer security team, we are used to patching the various Linux distros by applying numerous software patches. And the great news is that these updates are often times made available only a few days after the vulnerability is announced. It's what we have come to expect over the years, because several huge enterprises support the Linux operating system, investing generous amounts of money in it.
But now, we are facing a much more serious vulnerability, and it's one that can't be successfully patched through a software update. In fact, the available updates can fix some of the problems, but they will cause more trouble. Here's what has happened.
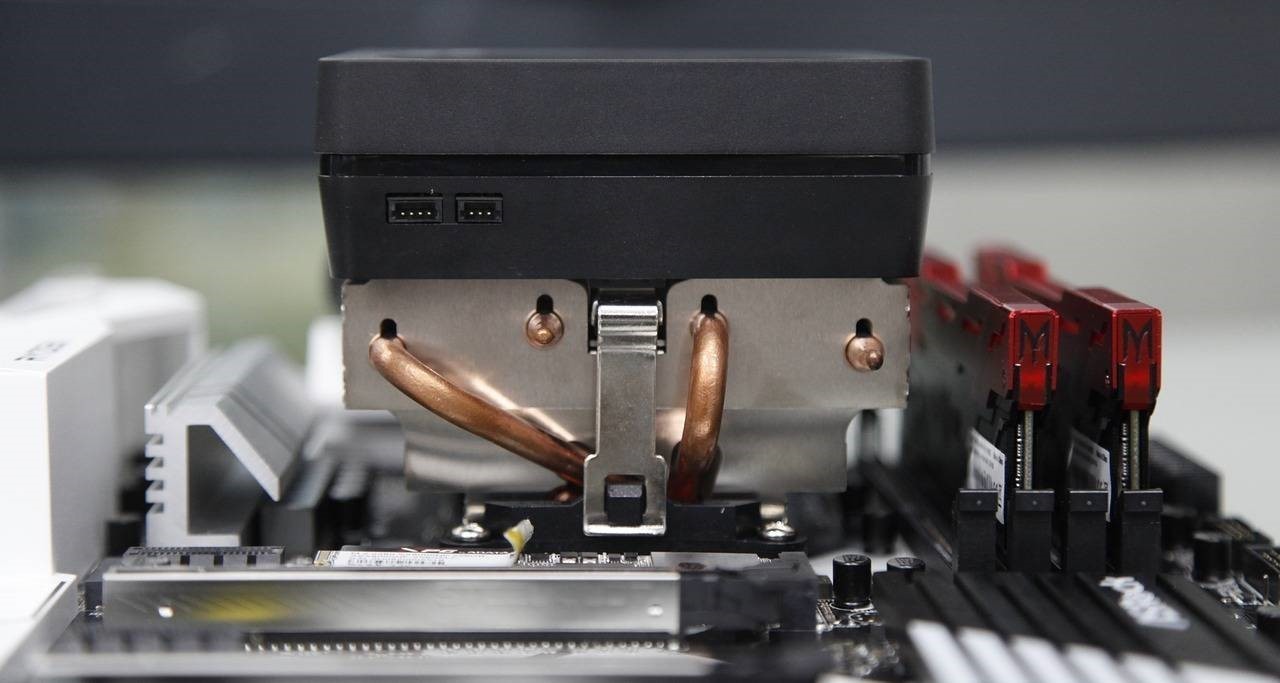
Whenever a computer application needs to output some data, it will tell the CPU to access the OS kernel, which is the only means of writing data to a file, for example. Then, when the process completes, the kernel will allow the application to regain control and continue to do its thing. Still, the data that was passed by the application to the kernel continues to be stored in a fixed virtual memory address space, because this increases the CPU processing speed.
The method has the potential to decrease access time in a significant way. In theory, it makes no sense at all to allocate a new range of memory cells, and then jump to a different memory address each time your application needs access to the kernel. So, this is the way in which almost all CPUs have been manufactured within the last decade.
Researchers have recently discovered a method that allows hackers to read the content of the kernel memory, though. And to make things even worse, this is the very place where your user passwords and access keys may be stored, for example. This means that a simple piece of JavaScript code that runs in your browser while you are visiting an infected website could read all the sensitive data that you have used to log into your online banking account.
But what is the immediate impact of this security flaw for regular business owners? First of all, most cloud computing service providers will be affected by this vulnerability. Think Amazon EC2, Microsoft Azure, Google Compute Engine, and so on; all the businesses that utilize the cloud may have their private data exposed.
Both Intel's and AMD's CPUs are affected. While most OS makers have already released patches for their products, the speed of most computers will be affected, because the updates force the CPUs to utilize different memory areas for each application call, whenever the kernel needs to take control.
Researchers have put up a dedicated website which presents two related vulnerabilities; here's the link to it. The first vulnerability was named Meltdown, and it affects mostly Intel CPUs, while the second one, codenamed Spectre, affects Intel, AMD and Arm CPUs.
Use this tool to determine if your computer is affected and/or properly patched. It's a Windows tool, because people running the Windows OS are also affected, but the tool will run fine under Wine as well.
People report that the speed of their patched computers has decreased by 5% to 30%. This can mean a lot and significantly slow down performance, especially if your computer utilizes an older CPU. Sadly, there is nothing else that you can do about it. Hopefully, modern generations of processors will run faster and won't have this vulnerability.